Introduction
This guide provides information on how to:
Set up Beyond Identity as a 3rd party IdP with Aruba CPPM for Wi-Fi Access.
Set up Aruba Instant AP (IAP) via Aruba Central Cloud to leverage Aruba CPPM and Beyond Identity SAML based flow for MFA. (l3 Authentication)
Prerequisites
Ensure that you have the following:
Administrator Access on Aruba CPPM to setup custom services and web logins.
Administrator Access to Aruba Central for configure Aruba Instant AP for external redirects.
Beyond Identity (BI) Admin Portal Access.
Devices with BI Platform Authenticator and a valid Passkey.
SAML Connection Between BI & Aruba CCPM
Configuration on Beyond Identity Admin Portal
Navigate to Integrations 🡪SAML🡪Add a SAML connection.
Configure a Name for the connection.
Set the value of the SP Single Sign On URL using the below format
Set the value of the SP Audience URL using the below format
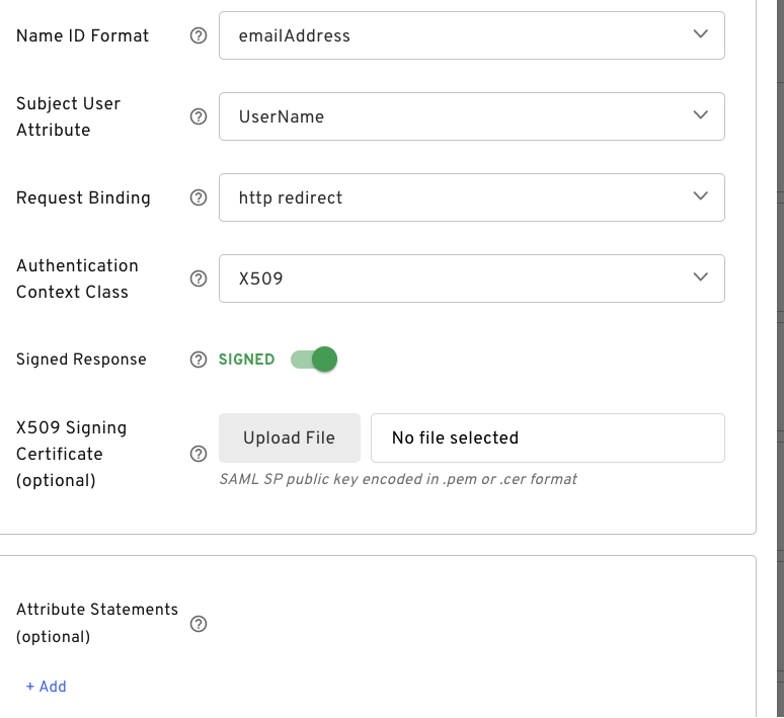
Set the remaining values as below and Save Changes
Note down the IdP SSO URL and download the certificate as shown below
.png)
Configuration on Aruba CPPM
Navigate to Administration🡪Certificates🡪Trust List🡪Add
Browse the Beyond Identity Certificate downloaded in the step 6 in the previous configuration and update the Usage as SAML and Others as shown below
.png)
Navigate to Configuration🡪Identity🡪Single Sign-On(SSO)🡪SAML SP Configuration.
Update the Identity Provider (IdP) URL with the value stored in step 6 in the previous configuration.
Under Enable SSO For check Insight and Guest.
Under IdP Signing Certificate select the Beyond Identity Certificate stored in the Trust store.
Hit Update to update the SAML settings.
.png)
Navigate to Configuration🡪Pages🡪Web Logins and Create a new Web Login
Provide a Name and Page Name
Under Login Form🡪Pre-Auth Check: Pick SAML Service Provider
.png)
Configuration on Aruba Central for IAP SSID SETUP
Navigate to Devices🡪WLANS🡪Add SSID
Under General tab input the ESSID name. ex: BYID-TEST
Under the security tab configure the below attributes.
Security Level: Visitors
Type: External Captive Portal
Captive Portal Profile: (Create new one as shown in step 4)
Primary server: Aruba CPPM FQDN
.png)
Create Captive Portal Profile as shown below
Name: Assign the name for the profile
Authentication Type: Radius Authentication
IP or Hostname: Aruba CPPM hostname
URL: Web Login Service Address ending in /guest/<pagename>.php
Captive Portal Failure: Deny Internet
Redirect URL: Any URL
.png)
Under Advanced Settings enable Mac Authentication for caching the mac-address.
.png)
Optionally Enable Accounting and point to the Acct server.
Under the Access tab set the Access rules to Unrestricted. (Role Based Access is handled by Aruba CPPM)
Navigate to Devices🡪Access Points🡪Security🡪Roles and Create a new role (ex: beyond-preAuth)
The Access rules in this newly created role should allow the following
Access to Clearpass (http/https)
DHCP/DNS
Apple CNA (captive.apple.com)
Access to Beyond Identity cloud (.byndid.com)
.png)
Workflow
Device Connects to the SSID configured for Beyond Identity for the first time.
Aruba AP does MAC-Authentication using RADIUS against CPPM using the client mac address.
Aruba CPPM invokes the Guest Mac Authentication service which has an enforcement profile (ex: Beyond-Guest Captive Portal Profile) that is configured to return a role name which matches the one configured in the IAP. (ex: beyond-preAuth)
.png)
.png)
Once the pre-auth role is assigned to the device its now connected to a captive portal at which point the IAP redirects the client to the web-login service which initiates the SAML flow with Beyond Identity.
At this point the SAML SP service is invoked in CPPM (ex: Cloud SAML Clearpass Admin SSO Login service with enforcement profile to instruct the device to perform full RADIUS auth)
.png)
After the SAML flow is complete the IAP is instructed to perform a full RADIUS authentication.
At this point the CPPM invokes a BEYOND Guest Access service (created earlier) for post auth which refers to an enforcement profile created to set the Mac address caching to a day or a month.
.png)
.png)
SAMPLE ACCESS TRACKER View
.png)